Jim Springer, owner of Dunkelberger’s Fine Jewelry, is heading into retirement.
In the Wake of the Cyberattack on Stuller, 5 Tips on Cybersecurity
From password security to tracking-number safety, here are five cybersecurity tips to keep in mind.

New York—Stuller was hit by a cyberattack over Thanksgiving weekend that delayed shipments, shut down the phone lines, and created other operational issues amid the holiday rush.
It took a few days for the massive manufacturer and supplier to get same-day shipping services on in-stock items and the phone lines back up and running.
While Stuller said there was no indication that sensitive business information was compromised—noting that customer credit cards on file are tokenized, encrypted, and not housed at Stuller—the stressful disruption came at the most critical time of the year for the supplier, underscoring the need for businesses today to invest in cybersecurity.
Stuller did not provide additional details on the specifics of the cyberattack.
In a COVID-19 world, and even before then, the ability to connect with customers online is crucial, whether one is running a consumer-facing retail store or a business-to-business operation.
Here are five expert tips on how to navigate the online world safely.
Ensure employees are adequately protected as they work from home.
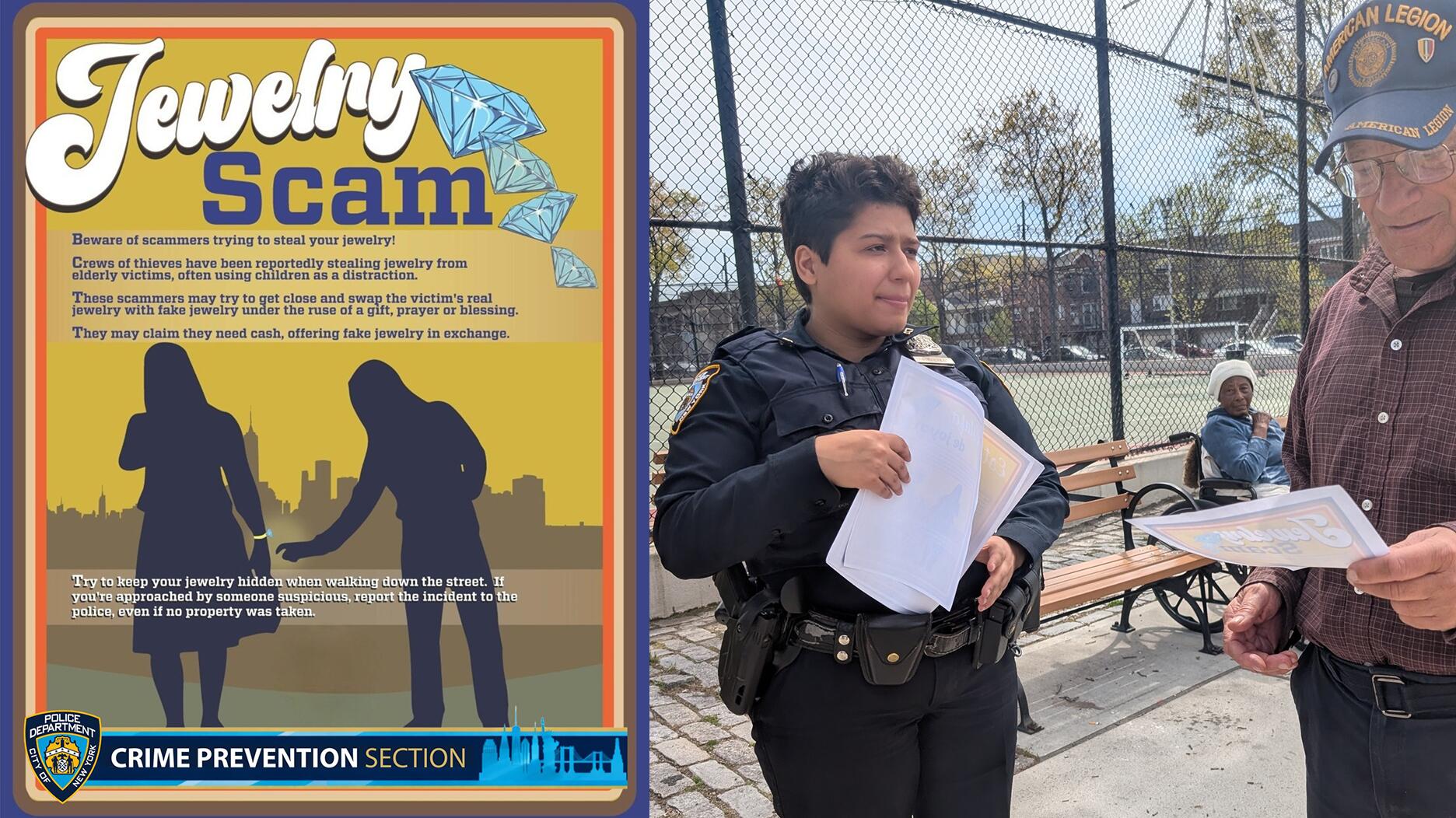
Law enforcement officials have seen an uptick in fraud and hacking now that more people are working from home on computers or smartphones less secure than those in their office, the Jewelers’ Security Alliance said in a recent memo.
Be sure all employees’ devices have updated protections in place, including firewall, malware, and spam protection.
Stop using the same password for everything.
JSA advises having “strong, unique” passwords.
When the password for everything is the same, it may be easy to remember, but it’s also easy for hackers to gain access to several accounts in one swoop.
Users may also want to set up two-factor or multi-factor authentication.
“If a cybercriminal were to gain access to your log-in credentials, they wouldn’t be able to compromise your account if they didn’t have access to a passcode that would be sent to your phone,” explained Ryan Ruddock, senior research assistant at JSA, during an October webinar on online scams.
If you’re unsure about an email, just don’t open it.
Be wary of email phishing scams, which are attempts to trick users into giving criminals access to personal information.
“The intention behind phishing is to acquire personally identifiable information. So that’s going to include credit card information, social security numbers, account log-in credentials, and, in some cases, intellectual property,” said Ruddock.
It’s the most common type of cybercrime, said Ruddock, noting that it doesn’t target specific individuals.
Criminals will send a mass email in the
Misspellings and poor grammar are red flags to look for in phishing emails, he said, but also be wary of any email sent with a sense of urgency, pressuring users to act now, think later.
If an email doesn’t look trustworthy, don’t open it or click on any links. Delete it.
If a link in what is believed to be a phishing email is clicked, Ruddock recommended disconnecting from the WiFi, which could prevent malware from being installed on your computer, running an anti-virus scan, and changing passwords.
Also, be on the lookout for email spoofing, which involves an email sent from an address that’s almost, but not quite, identical to a genuine email address for a contact.
An email might look like it’s coming from longtime vendor, such as JohnSmith@jewelry.com, but upon closer inspection, it may actually read JohnSmith@jewellry.com.
If anything about the email seems off, it’s best to contact the vendor or customer by phone and be sure the request is genuine, JSA said.
Be careful with tracking numbers.
For any questions about a transaction, it’s best to reach out to the customer by phone via the number given at the time of purchase.
“You do not want to use the number given to you by the caller,” advised Ruddock.
JSA does not advise giving out the tracking number on a shipment. If a tracking number of a package is given to someone other than the customer, it may be possible for that person to redirect the merchandise.
JSA has also seen cases where a caller, pretending to be from a retail store, contacts a supplier and requests that a high-end item be sent to the store. The caller later diverts the shipment to a different address.
Set a limit on the number of times an address can be changed on a shipment, said Ruddock, and be clear with the shipper about how change of address requests should be handled.
Some companies, he said, have specified to their shipping company that if there are any attempts to change the address, the package should instead be returned to the company.
Make sure employees know the company’s cybersecurity policy.
Every company should have a written cybersecurity policy that is read and signed by employees, said JSA.
Be sure to regularly review the cyber-protocols with employees so everyone is on the same page.
Select cyber security firms also offer tests that allow employers to determine their employees’ ability to avoid phishing attacks and other scams.
Provide additional training to those employees who need it, advised Ruddock.
For more information about cybersecurity, visit the JSA website.
The Latest

When conducting its May consumer confidence survey, The Conference Board asked extra questions about consumers’ budgeting strategies.
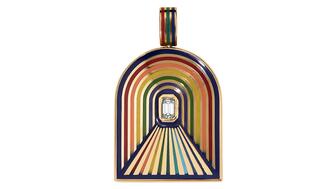
The “Tunnel” charm, our Piece of the Week, celebrates Pride Month with its design inspired by hope and the light at the end of the tunnel.

As gold prices rise, today’s retailers are looking for alternatives at prices that will appeal to wider audiences.

The jewelry industry is reassessing its positioning as Gen Z reshapes the retail landscape and lab grown continues to gain market share.


Up for auction at Sotheby’s, the collection of Tempelsman’s personal effects includes a Cartier Tank watch Jackie O. gifted him.

The Miami-based fine jewelry brand will host its first summer residency in the Colorado mountain town from June 5 to Aug. 23.
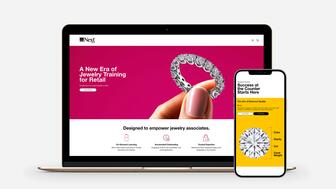
With the trade and customer trust in mind, GIA® developed NextGem™ – on-demand training designed specifically for retail.

The organization also announced its international board of directors for the 2026-2027 term.

Saks Global confirmed the closure this week, spelling the end for a store that’s been part of downtown Dallas for more than 100 years.
Smith discusses how managers should handle a top performer's exit, warning that a poor response could have a lasting impact.
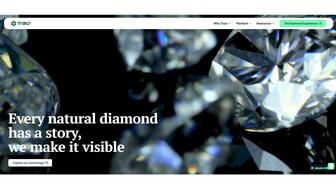
The Gemological Institute of America is now a 30 percent stakeholder in Tracr, the De Beers-backed blockchain for diamonds.

The retailer is bringing Rolex Certified Pre-Owned watches to five U.S. cities in 2026 for collectors to see, try on, and purchase.

The actress and entrepreneur stars in the jeweler’s new campaign that celebrates life’s quiet moments.

The price of gold has risen, affecting the number of pieces designers make, the materials they use, and how they position themselves.

The jewelry retailer is zeroing in on Zales, Jared, Kay Jewelers, and Blue Nile as it looks to create unique brand identities for each.

Dr. Akinwumi Adesina, a development economist, will head the fund created to help Botswana diversify its economy.

Sotheby’s has appointed the former Phillips executive as its global head of private sales and retail in its watches division.

A private collection of five Paraíba tourmalines also will be up for sale at Sotheby’s High Jewelry auction in New York, scheduled for June 16.

From Gen Z’s view of luxury to “doom spending,” these are the six consumer trends to note this year.

The show started by honoring Mildred Marcano, ended with a tearful Beth Anne Bonanno, and recognized a dozen-plus designers in between.

The revamped online diamond marketplace will feature pricing intelligence and data-driven tools for more efficient buying and selling.

The miner said demand for higher-quality emeralds is stable, but there is notable caution in the market.

The “River of Heaven” necklace, our Piece of the Week debuting at Couture, combines 26 salt and pepper diamonds spaced by Tahitian pearls.

This year’s inductees include second-, third-, and fourth-generation jewelers.

The author, speaker, and entrepreneur will give his presentation, “Spiritual Billionaire,” on Saturday morning.

Three-time Grammy award-winning artist Nelly is set to perform at the annual event at Tao Beach on Sunday night.